Modern manufacturing systems are increasingly vulnerable to cyberattacks that do more than steal data or encrypt files. The Tech Xplore article highlights emerging research showing that attackers can deliberately trigger shutdowns across industrial environments, disrupting production at scale and exposing deeper weaknesses in cyber-physical systems.
These attacks target the tightly integrated networks that control factories producing everything from electronics and spacecraft to medical devices and automobiles. When compromised, the consequences ripple far beyond a single facility, affecting supply chains, economic stability, and even national security. Researchers emphasize that such disruptions are not hypothetical; they reflect a growing trend where operational technology becomes a primary attack surface rather than traditional IT systems.
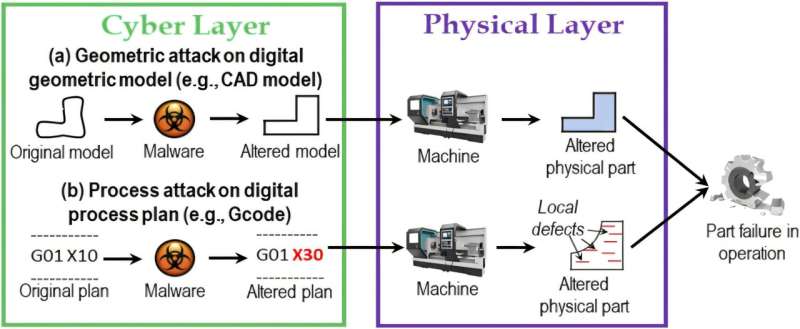
Unlike conventional cyber incidents, which focus on data breaches or ransomware, these newer threats exploit the coordination mechanisms that keep industrial processes running. By interfering with control systems, attackers can halt machinery, degrade performance, or force emergency shutdowns. In highly automated environments, even minor disruptions can cascade quickly, leading to large-scale production losses.
The research underscores a shift in cybersecurity priorities. Protecting industrial systems now requires safeguarding not just information, but also the timing, synchronization, and physical processes that underpin automated operations. Earlier studies have shown that subtle manipulations, such as altering system timing, can destabilize entire networks while remaining difficult to detect.
As industries adopt more connected and autonomous technologies, the attack surface continues to expand. Cyber incidents are no longer isolated technical failures but systemic risks with societal consequences. Disruptions to manufacturing can affect critical goods, infrastructure, and public services, amplifying the impact far beyond the initial breach.
The findings point toward a need for more resilient system design, including layered defenses that integrate real-time monitoring, anomaly detection, and stronger safeguards for industrial control systems. As cyber threats evolve, ensuring continuity of operations may become as important as protecting data itself.
