Doctoral student Hala Ali and her co-authors from Virginia Commonwealth University and cybersecurity firm Volexity introduce their research in the paper “Leveraging Memory Forensics to Investigate and Detect Illegal 3D Printing Activities.” Their work addresses a growing challenge: criminals are increasingly using 3D printers to manufacture weapons or other illicit items because the practice is cheaper, less regulated, and harder to trace, tells Tech Xplore.
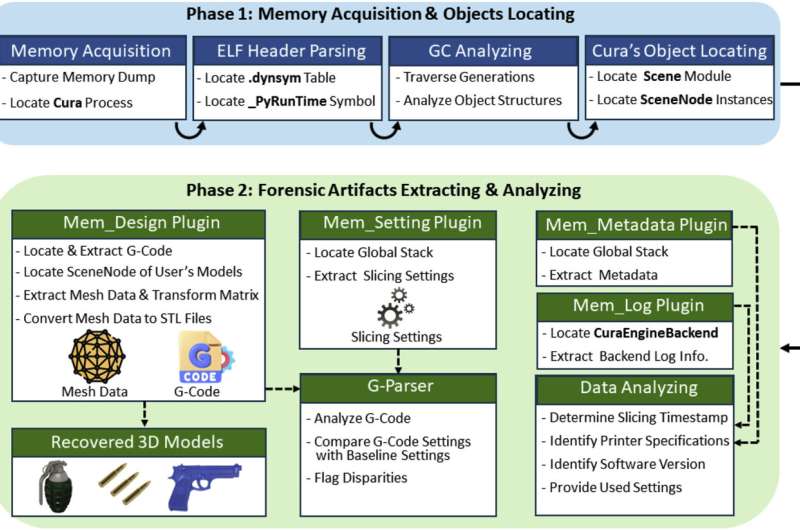
The core of their method is a framework called SliceSnap. It focuses on the memory of “slicing software,” the programs that convert 3D digital models into the layer-by-layer instructions (G-code) a printer executes. By analyzing residual data in memory, SliceSnap can recover deleted or hidden slicing files, metadata, and G-code text that might otherwise be erased or overlooked. This enables investigators to determine if a 3D printer was used to produce an illicit item by tracking what was printed, how, and when.
The article highlights practical implications. One example: the slicing application Ultimaker Cura, used by over a million people globally, presents a complex software footprint. Manipulations in G-code, such as altering fan speed or layer structure, can transform an otherwise innocuous object into one with harmful capabilities. Recognizing that fact, Ali’s team used SliceSnap to identify hidden traces and reconstruct what was printed.
Their research has gained national recognition; Ali won best paper at the 25th annual Digital Forensics Research Conference in Chicago. While it does not eradicate the challenge of illicit 3D printing overnight, the work advances forensic capability in a domain where regulation and tracking have previously lagged behind technology. It underscores the need for forensic science to keep pace with additive manufacturing’s evolving threat surface.
